How Does EDR Improve Cybersecurity?
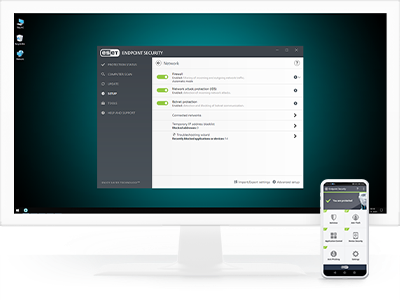
Endpoint Detection and Response (EDR) is a critical component of modern cybersecurity strategies, providing advanced protection against a wide range of cyber threats. Endpoint detection and response EDR solutions focus on monitoring, detecting, and responding to threats that target endpoints, such as computers, mobile devices, and servers.
Continuous monitoring and visibility:
EDR solutions provide continuous monitoring of endpoints, offering real-time visibility into activities across the network. This constant surveillance helps in identifying suspicious behavior and threats as they emerge. Unlike traditional antivirus software, which may only scan periodically, EDR ensures that every action on an endpoint is scrutinized, making it harder for threats to go undetected.
Advanced threat detection:
EDR uses sophisticated algorithms, machine learning, and behavioral analysis to detect advanced threats, including zero-day vulnerabilities, ransomware, and fileless malware. These threats often bypass traditional security measures, but EDR’s advanced detection capabilities can identify anomalies and malicious activities based on patterns and behaviors. By doing so, EDR can detect threats that signature-based antivirus solutions might miss.
Rapid incident response:
One of the primary advantages of EDR is its ability to facilitate rapid incident response. Once a threat is detected, EDR solutions can automatically isolate the affected endpoint, preventing the spread of malware across the network. They also provide detailed forensic data and analysis, helping security teams understand the nature of the attack and respond swiftly. This quick containment and response are crucial for minimizing damage and reducing downtime.
Improved forensics and investigation:
EDR tools collect and store extensive data from endpoints, including logs, file modifications, network connections, and user activities. This wealth of information is invaluable for forensic investigations, enabling security teams to reconstruct the sequence of events leading up to an incident. Improved forensics help in identifying the root cause of an attack, understanding the attack vectors, and implementing measures to prevent future occurrences.
Automated threat mitigation:
Many EDR solutions offer automated threat mitigation capabilities. This includes executing predefined responses to detected threats, such as quarantining files, blocking network access, or removing malicious software. Automation reduces the reliance on manual intervention, allowing for faster and more efficient threat neutralization. This proactive approach helps in maintaining business continuity and protecting critical assets.